
A New Era of Cybersecurity Risks: The Impact of Deepfakes
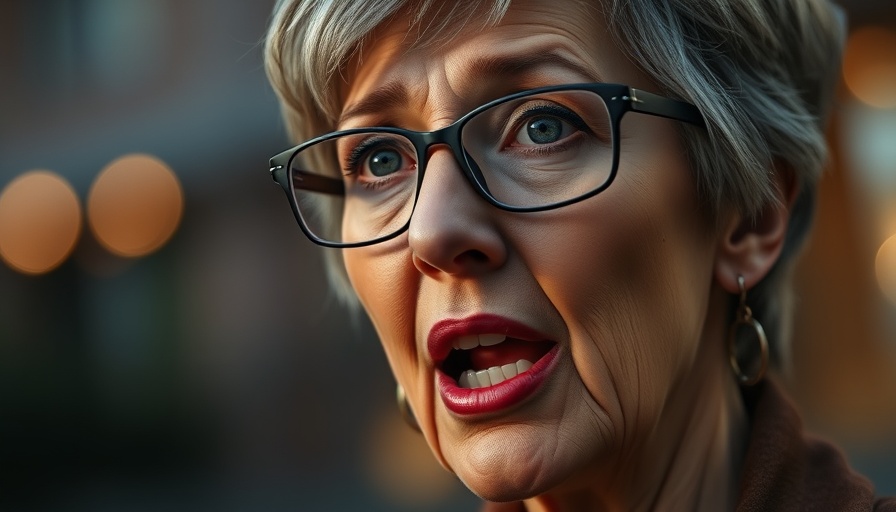
In a startling turn of events, the FBI is currently investigating a sophisticated phishing campaign that may have used advanced deepfake technology to impersonate Susie Wiles, the chief of staff to former President Trump. This incident not only raises alarming questions about the vulnerability of high-level government officials but also reflects a growing trend in the misuse of AI-generated content.
Deepfakes have become a cornerstone of modern cybersecurity threats, leveraging machine learning algorithms to create hyper-realistic impersonations of individuals. In this case, high-profile Republicans and business executives received fraudulent communications that appeared to originate from Wiles, which could have serious implications for both personal privacy and national security.
Understanding Phishing: A Legacy of Evasion
Phishing remains one of the most effective tactics employed by cybercriminals. With the rise of deepfake technology, the ability to convincingly impersonate individuals only escalates these threats. Jake Williams, a former NSA hacker, pointed out that this kind of social engineering is an unsolicited reminder for those in power: "This is the type of garden-variety social engineering that everyone can end up dealing with these days, and certainly top government officials should be expecting it." By disrupting trust between key figures, hackers can manipulate not just individuals but the broader political landscape.
Behind the Curtain: The Mechanics of a Phishing Attack
How do attackers build a target list for such elaborate scams? Authorities suggest that Wiles' personal phone may have been hacked, granting hackers access to her contacts. However, it is equally possible that criminals sourced information from public profiles or data sold on the gray market. This case highlights a crucial aspect of modern cybersecurity: the need for robust information protection and data privacy regulations that safeguard against such intrusions.
Lessons Learned: Security Awareness in High Places
What does this incident reveal about security practices among those in the upper echelons of political power? Wiles' experience may hint at a broader issue: an unsettling level of security awareness among top officials. Their need for transparency and communication often overshadows fundamental cybersecurity measures. Enhancements in security training and protective technologies are essential, as emphasized by experts in the field. Combining awareness with technology can build a formidable defense against future threats.
The Future of Cybersecurity: Predictions and Precautions
As deepfake technology continues to evolve, cybersecurity professionals anticipate even more aggressive and innovative phishing tactics. Future predictions indicate a potential increase in the personalization of attacks, making them harder to detect and more damaging when executed successfully. This evolving landscape necessitates continuous vigilance from both organizations and individuals to stay ahead of adversaries.
How to Protect Yourself: Practical Insights for Everyone
While high-profile figures often believe they are more attractive targets, the reality is that many phishing techniques can trick anyone. Here are several actionable steps individuals can take to protect themselves:
- Regularly update passwords and use two-factor authentication to secure accounts.
- Be cautious about sharing personal details online, as this can fuel social engineering attacks.
- Educate yourself and others on recognizing common phishing tactics, including suspicious emails and unexpected calls.
- Utilize security tools and software that detect fraudulent activity and educate on safe web practices.
Conclusion: Navigating the Digital Landscape
As deepfake technology and phishing tactics grow increasingly complex, being informed and prepared is critical. Each individual, whether a public figure or a private citizen, has a role in enhancing the collective cybersecurity landscape. By applying the lessons learned from this incident, we can work toward a safer digital future.
Engage with your community and share knowledge about cybersecurity practices. Awareness and proactive measures are our best defenses against the evolving threats of digital deception.
 Add Row
Add Row  Add
Add 



Write A Comment